
This guide will provide you with the necessary steps to address the problem of SSH not functioning properly in macOS Ventura. SSH, which stands for Secure Shell, is a network protocol that enables secure communication and data exchange between two computers via servers. Due to its encryption, it is the preferred method, especially on vulnerable networks. macOS already comes with a built-in SSH client called Terminal.
SSH operates on a client-server model that enables you to establish a connection between an SSH client instance and an SSH server. However, lately, users of the latest macOS are experiencing difficulties with SSH. Several reports indicate that SSH is not functioning correctly in macOS Ventura. As a consequence, users cannot log in to their Ventura-powered Macs from devices with outdated keys. Additionally, some users are receiving an error message stating "no matching host key type found." So, what is causing these issues?
One possible explanation for these issues is that Ventura comes with OpenSSH_9.0p1, which "disables RSA signatures using the SHA-1 hash algorithm" by default. To address this problem, advanced users may choose to generate keys that use a more secure hash algorithm. However, beginners can use a simple workaround that we've outlined below. Let's go through it together.
How to fix the issue of SSH not functioning in macOS Ventura?
- Open the Finder and use the keyboard shortcut Shift+Command+G to access the "Go to Folder" dialog box.
- Type the following location into the box and press Enter (Alternatively, you can navigate manually to the location via Macintosh HD > etc > ssh):
/etc/ssh/
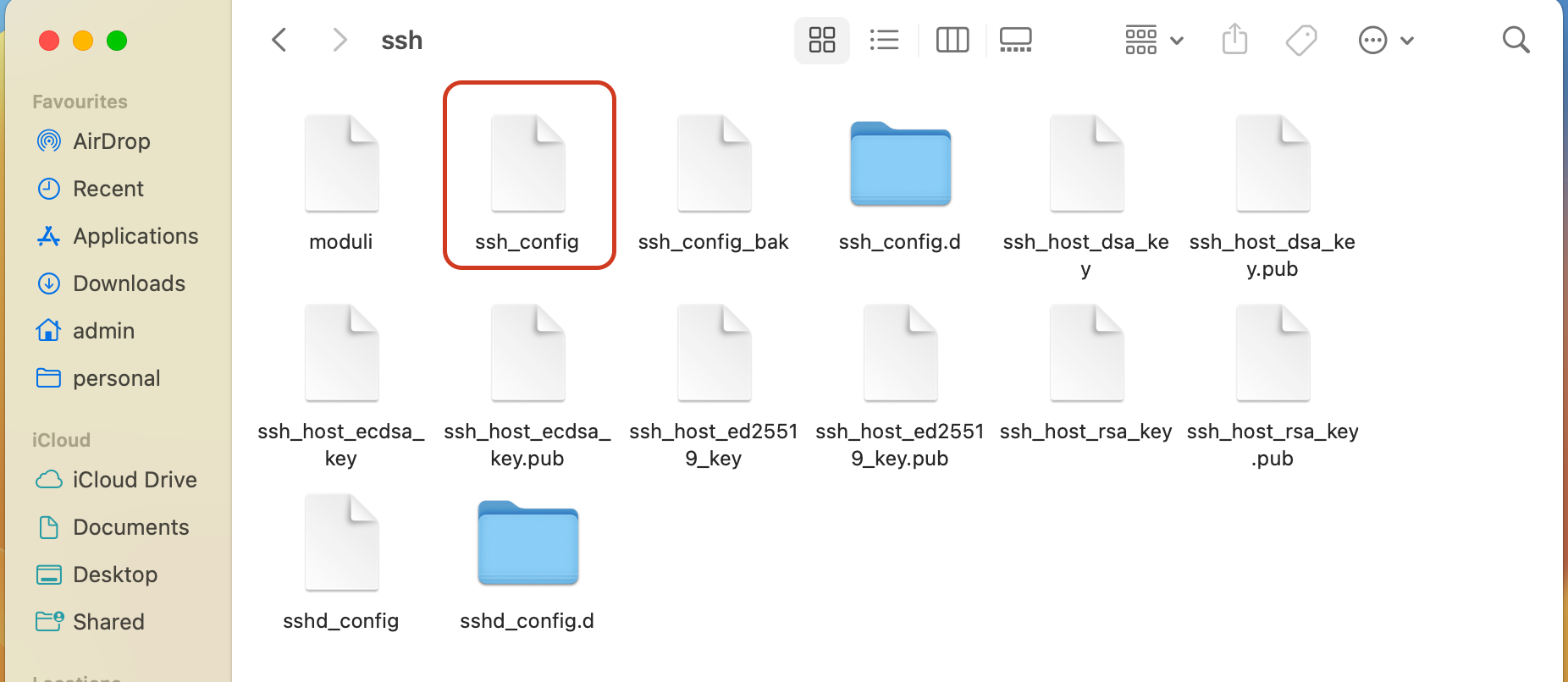
-
Copy the ssh_config file and save it as a backup in a different location.
-
Open the original ssh_config file and add the two following lines at the end of the file:
HostkeyAlgorithms +ssh-rsa
PubkeyAcceptedAlgorithms +ssh-rsa
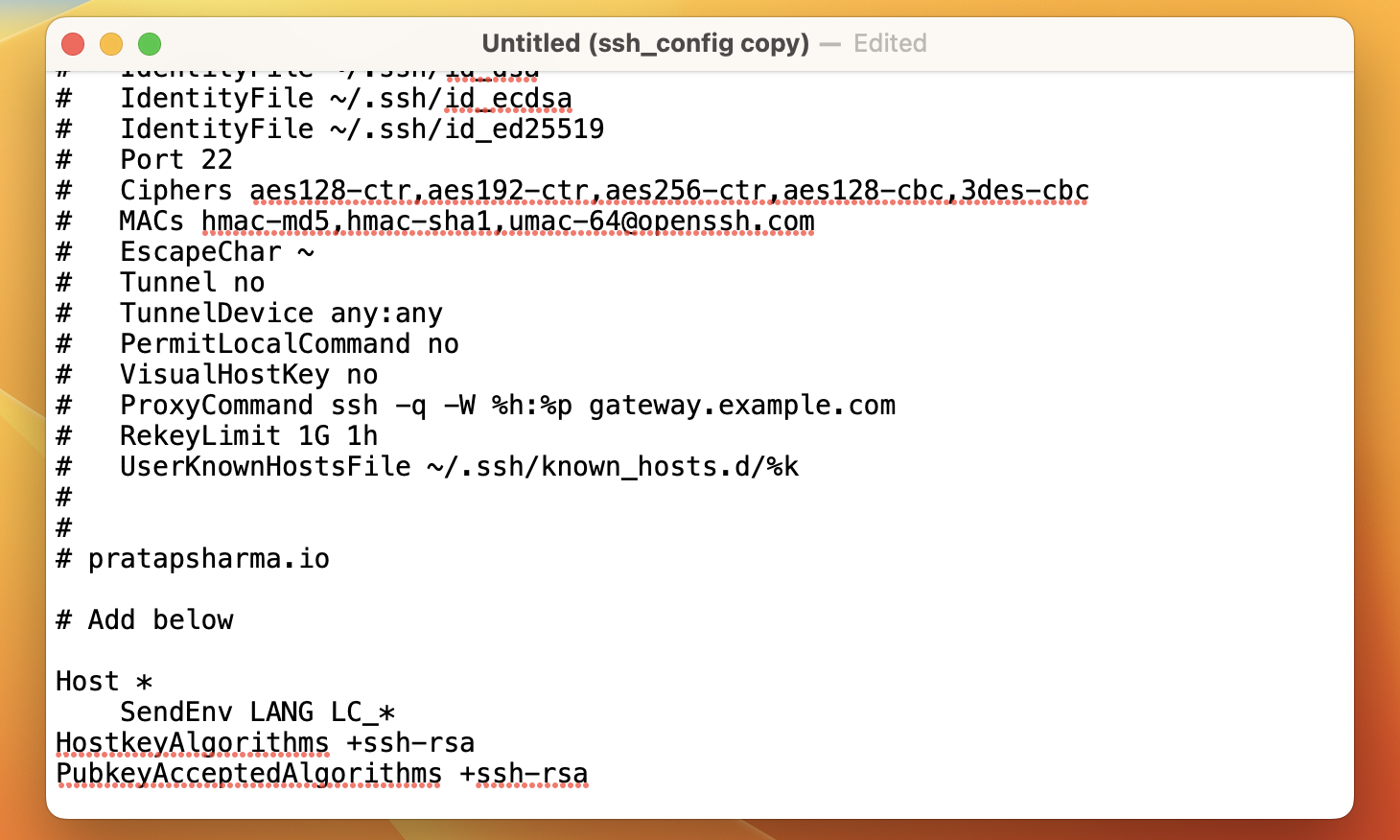
- After making the changes, press the Command+S keys to save the modifications.
Conclusion
That concludes the steps for resolving the problem of SSH not working in macOS Ventura. If you have any questions about the steps outlined above, please leave them in the comments section. We will respond with a solution as soon as possible.
You may also like my other articles:
- Why is System Design Important?
- Building Real-time Applications with Redis Pub/Sub
- Understanding Proxies: The Differences Between Forward and Reverse Proxies
💌 If you'd like to receive more tutorials in your inbox, you can sign up for the newsletter here.
Please let me know if there's anything else I can add or if there's any way to improve the post. Also, leave a comment if you have any feedback or suggestions.

Discussions